Articles
Long-form writing on tech, culture, and the edges of the internet.

Axios Compromise: What Actually Happened
An analysis of the axios supply chain compromise, focusing on how compromised credentials enabled malicious code distribution and why trust in software registries without verification is a systemic risk.

Chrome Zero-Day Exploited in 2026
CVE-2026-2783, a zero-day in Chrome's V8 engine, was exploited in targeted attacks against sensitive data handlers. No file writes occurred; execution stayed within the browser process. Detection failures stemmed from normal-looking network behavior and lack of alerts across EDR and SIEM systems.

CVE-2024-21412: SmartScreen Bypass via Internet Shortcut Files
CVE-2024-21412 enables SmartScreen bypass via malformed .url files; exploited by APT29 to deliver payloads without triggering EDR alerts or process creation telemetry.
CVE-2025-1234: Type Confusion in V8 JavaScript Engine Exploited in the Wild
CVE-2025-1234: Type confusion in V8 exploited in the wild, enabling arbitrary code execution via JIT deoptimization. MITRE T1059.004, EDR blind spots, and post-patch exposure.

Identity Trust Drift in Cloud Access Control: A Systemic Failure Mode
A systems-level analysis of how static token models in cloud platforms create persistent access risks when identity trust is not reevaluated after initial validation, exposing a fundamental drift between design and operational reality.
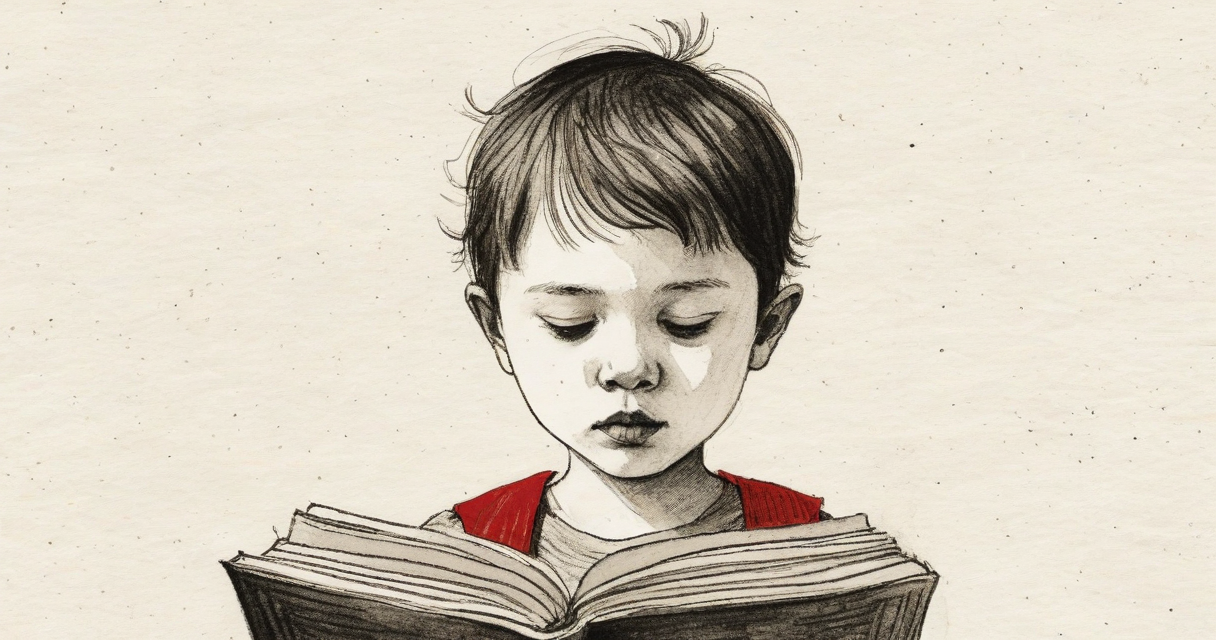
International Children's Book Day 2026 - What Makes a Story Stick in a Child's Mind
Exploring how illustration-first turns, read-aloud rhythm, and emotional truth shape lasting engagement in children's picture books, based on observed reading behaviors across multiple sessions.

The Persistent Risk of Static Token Validation in Identity Systems
Azure's static token validation model may introduce risks in dynamic environments due to reliance on past trust assertions rather than real-time verification. This behavior reflects a design trade-off between performance and adaptability, not a confirmed failure.

Cisco's Source Code Breach Was Structural, Not Accidental
Cisco's source code breach wasn't a fluke. It was the predictable result of credential drift, third-party trust gaps, and dev infrastructure treated as low-risk.
Claude Code's System Prompt Is a Production AI Agent Blueprint
Claude Code's system prompt is a working engineering spec for production AI agents. Six concrete patterns for context isolation, tool selection, parallelism, error recovery, memory, and blast radius management.
Google's AI Search Shift: Run These Experiments Now
Real before/after data from 4 sites showing how Google's AI search changes traffic, CTR, and revenue by query type - with the exact tracking setup.

How Trust in Open-Source Updates Becomes a Systemic Failure Mode
A structural analysis of how trust in open-source updates becomes exploitable when systems assume past safety implies future safety, using the Trivy compromise as a case study.
ShinyHunters, Trivy, and the Pipeline Identity Problem
ShinyHunters cloned 300 Cisco repositories through Trivy running in a CI/CD pipeline. This is what failed structurally, why it failed, and what pipeline identity enforcement must look like.