Internship orders interns to install cracked Burp
A cybersecurity internship told interns to install cracked Burp Suite Pro. Here is what that directive actually means and why the operator must refuse it.
1. Opening position
A cybersecurity internship is instructing trainees to install a cracked build of Burp Suite Pro on the systems they will use to perform security work. That instruction is not normal. It is a defect in the program, and it transfers the legal, operational, and integrity risk of that defect onto the intern.
Cracked software is a tampered binary obtained outside the vendor distribution path. The license enforcement has been removed, which means the build has been modified by an unknown party. Burp Suite Pro is a commercial product sold by PortSwigger under a per-user license. There is no condition under which a paid commercial tool, modified by an unauthorised third party, becomes acceptable infrastructure for a regulated security function.
The question being asked is whether this is industry standard. It is not. The fact that the question has to be asked is the finding. A program that cannot supply licensed tooling to its own interns has already failed the threshold test for handling client data, customer systems, or production access of any kind.
2. What actually failed
The internship program is directing personnel to introduce an unverified executable into the workstation that will subsequently be used to test other systems. The tool that the intern is being told to install is the same tool that will hold credentials, session tokens, intercepted traffic, and target scope data. The trust boundary of every engagement the intern touches now starts inside an untrusted binary.
The license violation is a separate failure on top of that. PortSwigger sells Burp Suite Pro per user, and the program is bypassing that contract. The legal exposure does not sit with the program alone. It sits with the individual operator who installed and executed the build, and with any client whose data is processed through that build. This is not a procurement oversight. It is a directive issued by the people running the program.
A further failure is what the directive teaches. The intern is being trained on a workflow where the tooling chain is unlicensed and unverifiable as a default operating condition. That workflow is being normalised at the start of a career. Whether the program retains that posture beyond the internship is not confirmed. What is confirmed is that the entry-level standard being set is one that no mature security function will accept.
3. Why it failed
The direct mechanism is the absence of a licensing and software supply control inside the program itself. Burp Suite Pro carries an annual per-seat cost. A program that cannot or will not absorb that cost for the people it deploys against client-adjacent work has chosen to externalise the gap onto the operator. The control that should exist (a procurement and provisioning path for vetted, licensed security tooling) is not present. It has been replaced with an instruction to source the tool from outside the vendor channel.
The second mechanism is the absence of a software integrity control. Cracked binaries are redistributed through forums, file lockers, and mirror sites. The modifications required to defeat licensing involve patching the executable. Anything else added during that patching is undetectable to the end user without independent reverse engineering. The program is not performing that reverse engineering. The intern is not performing it. No party in this chain is validating what the binary does beyond launching the GUI. The integrity check that should gate a security tool entering an operator workstation does not exist in this program.
The third mechanism is the absence of a governance control over what interns are told to do. A directive to install pirated software on a security workstation should not survive contact with a functioning policy, a functioning legal review, or a functioning technical lead. That it was issued at all means none of those layers are enforcing. Whether those layers exist on paper is not confirmed. Their effective state is observable in the directive itself. Controls that are not enforced are not controls. The program is operating without them.
4. Mechanism of Failure or Drift
The drift mechanism here is normalisation through onboarding. An operator’s earliest professional instructions become the default behaviour they carry forward. When the first authorised act of a security career is the installation of a tampered binary issued by an internal authority, the threshold for tool integrity is set at that level. Subsequent decisions inherit the threshold. The operator does not relearn it at every engagement. They calibrate against what they were told was acceptable on day one.
The second drift mechanism is the substitution of authority for verification. The intern was told to perform this action by the program. The directive carries institutional weight, which displaces the validation the operator should be running independently. In a security function the chain of trust is supposed to terminate at a verified source. Here, the chain terminates at a human instruction. The binary is trusted because someone with a title said to trust it. That is the same trust pattern that phishing exploits at scale.
The third drift mechanism is the export of risk to parties downstream of the program. The intern does not own the client engagement, the data the tool processes, or the network the tool reaches. Those belong to whichever organisation the program is delivering to. The cracked binary will execute against systems and data outside the program’s perimeter. Whether the program has disclosed this configuration to those downstream parties is not confirmed. If it has not, the program is supplying compromised operators to unaware recipients. That is the failure mode the original directive sets in motion.
5. Expansion into Parallel Pattern
The same mechanism produces failures outside this specific tool and this specific program. Any environment that issues an instruction to install software outside the vendor channel creates the same condition. Internal portals that ship modified installers, build pipelines that pull from unverified mirrors, contractor laptops provisioned with unlicensed tooling. The underlying control gap is identical. There is no procurement path, so the procurement path is delegated to the operator, and the operator’s only signal is the instruction itself.
The pattern repeats inside development and security environments where the cost of licensed tooling is treated as optional overhead. Static analysis tools, decompilers, mobile device frameworks, traffic interception proxies. Each one has a licensed channel and an unlicensed parallel. When organisations decline to fund the licensed channel, the unlicensed parallel becomes the default. The binary running on the workstation is not the binary the vendor ships. The behavioural difference between those two binaries is not measured by the organisation deploying them. The operator is the only point at which divergence would be detected, and the operator has been instructed not to look.
The pattern also repeats in how attacker tradecraft is supplied. The same forums and file lockers that distribute cracked commercial security tools distribute cracked commercial software in every other category. A workstation calibrated to source one tool from that channel is calibrated to source the next tool from it. The path is the same. The integrity gap is the same. The control that is missing is the same. There is no enforced gate between an untrusted source and an executing workstation. The internship directive is one instance of a structural problem that scales wherever procurement is treated as a discretionary expense.
6. Hard Closing Truth
A security program that runs on tampered tooling is not a security program. It is a liability operating under a security label. The directive in question is not a minor breach of policy. It is the program declaring, in writing, that it does not enforce the controls it is being paid to deliver. The intern is the first person to encounter that declaration. They will not be the last.
The legal posture is unambiguous. Burp Suite Pro is a licensed product sold by PortSwigger on a per-user basis. Installing a cracked build is a copyright violation by the installer. The fact that the installation was directed by the program does not transfer the violation away from the operator. It compounds it. The operator is now in possession of an unlicensed commercial binary on a workstation that will touch client systems. Any incident traced back to that workstation begins with a finding that the operator was running unlicensed, tampered software at the time of the engagement.
The operator position is to refuse the directive and document the refusal in writing. A program that cannot fund seat licenses for the tools its interns are required to run cannot be trusted with the engagements those interns will be assigned to. The correct path is to use Burp Suite Community edition, request a PortSwigger-issued license through the program, or escalate the directive to a party outside the program. If the program retaliates against that refusal, the program has confirmed what the directive already indicated. Identity is the boundary. Tool integrity is the boundary. A program that violates both at induction has nothing further to teach.
Keep Reading
 cloud sovereignty
cloud sovereigntyMicrosoft disclaims European sovereign cloud under oath
Microsoft's France legal affairs director told the Senate under oath he cannot guarantee European sovereign cloud data stays out of US reach.
 vulnerability management
vulnerability managementNVD stopped, your scanner didn't notice
NVD enrichment is no longer keeping pace with CVE volume. What that breaks inside vulnerability management programs, and what operators must now own.
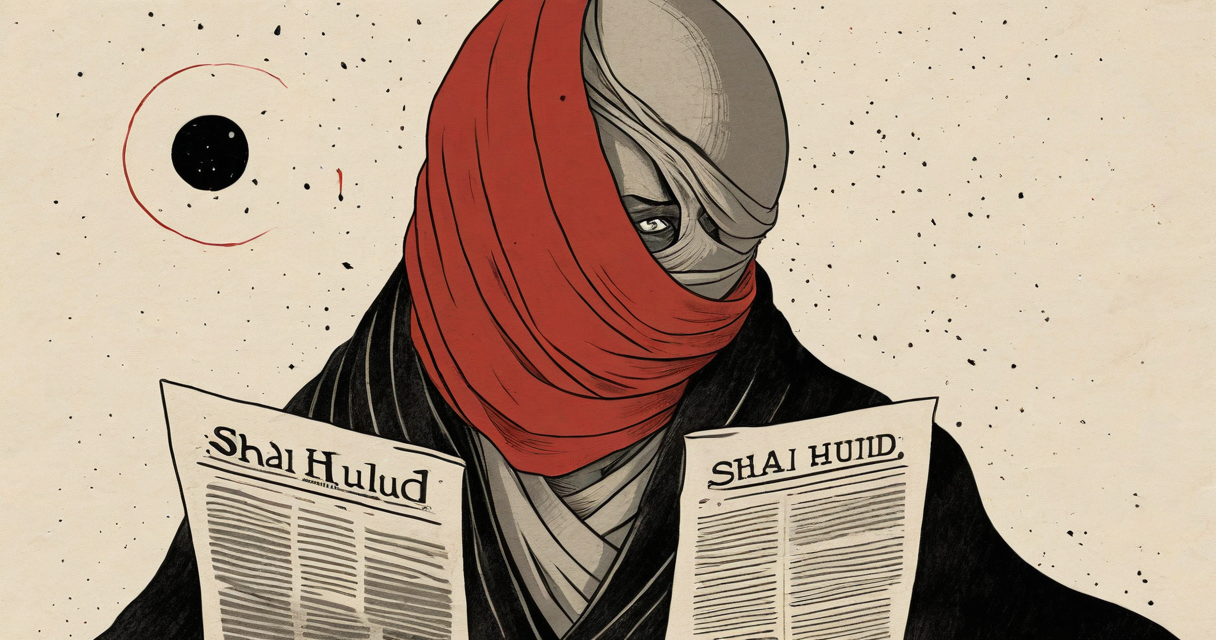 shai-hulud
shai-huludShai-Hulud goes public
Shai-Hulud worm published to GitHub by teampcp. What is confirmed, what is not, and the publication interval that matters.
Stay in the loop
New writing delivered when it's ready. No schedule, no spam.